G Wireless Network Security Configuration for Critical Infrastructure
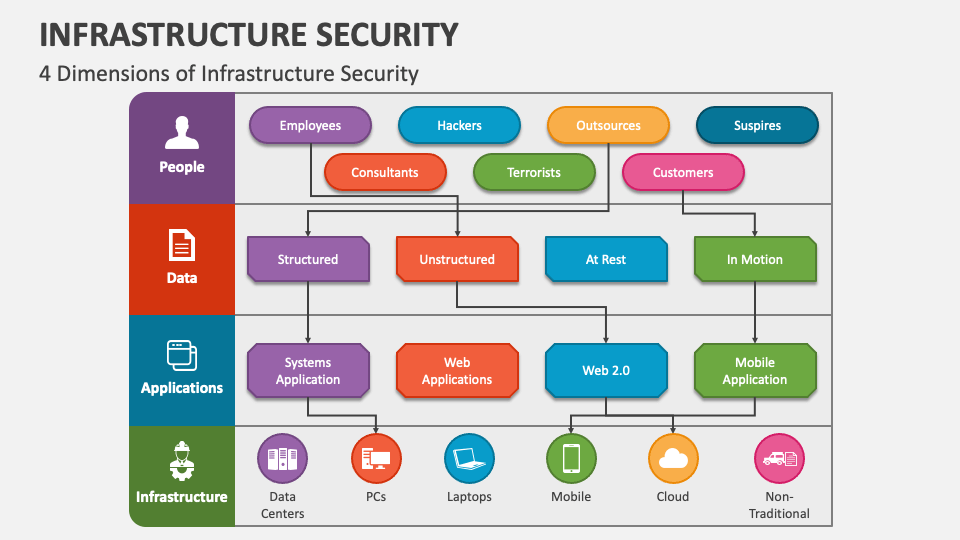
The security of critical infrastructure is a top priority for organizations and governments around the world. As the reliance on wireless networks continues to grow, the need for robust security configurations becomes increasingly important. This article will explore the importance of G wireless network security configuration for critical infrastructure and provide best practices for ensuring the security and integrity of these networks.
Understanding the Risks of Unsecured Wireless Networks
- Unauthorized access: Unsecured wireless networks can be accessed by unauthorized individuals, leading to data breaches and cyber attacks.
- Interference: Interference from other wireless devices can cause network downtime and decreased performance.
- Denial of Service (DoS) attacks: DoS attacks can flood a network with traffic, causing it to become unavailable to users.
Best Practices for Securing G Wireless Networks
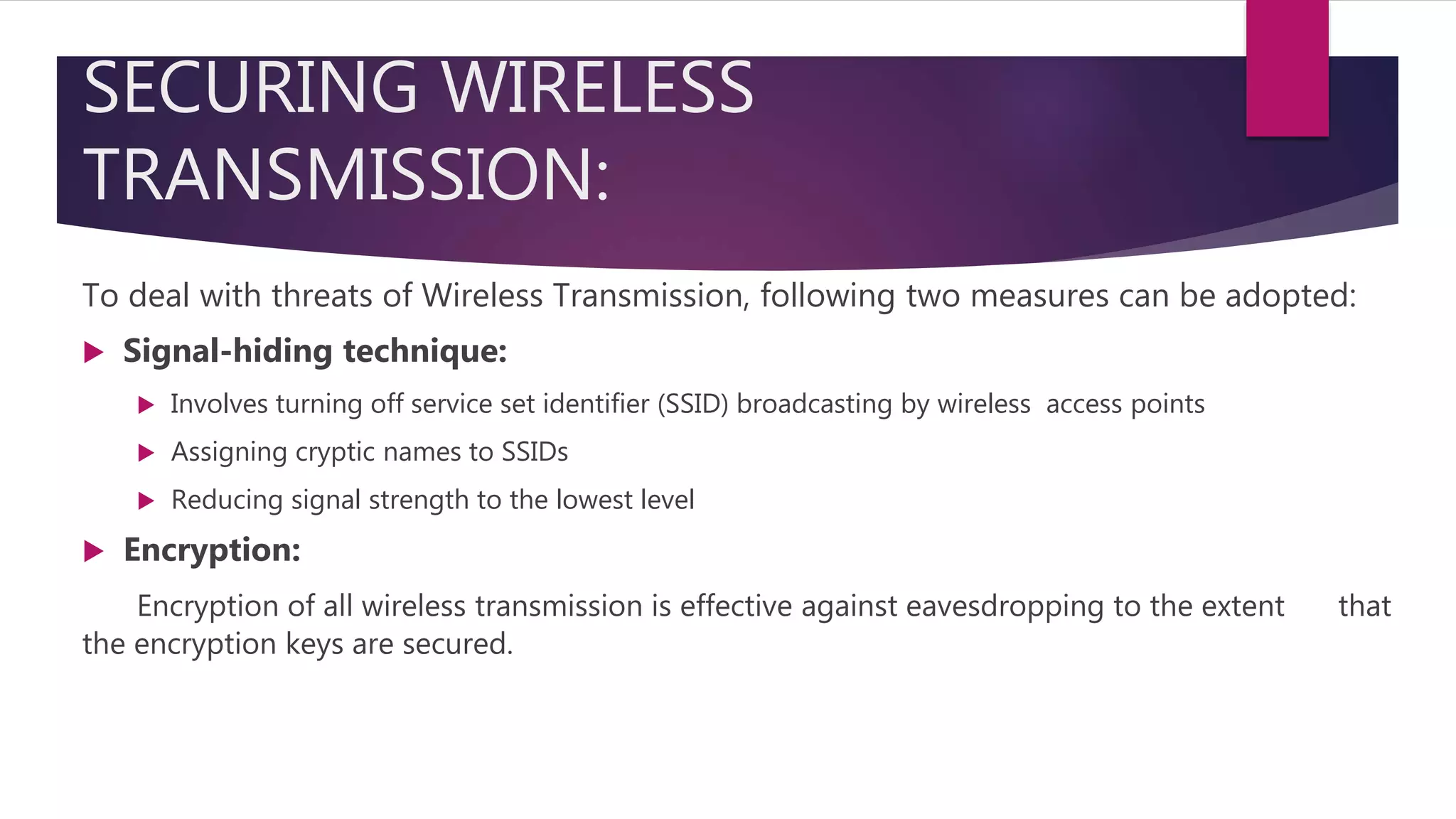
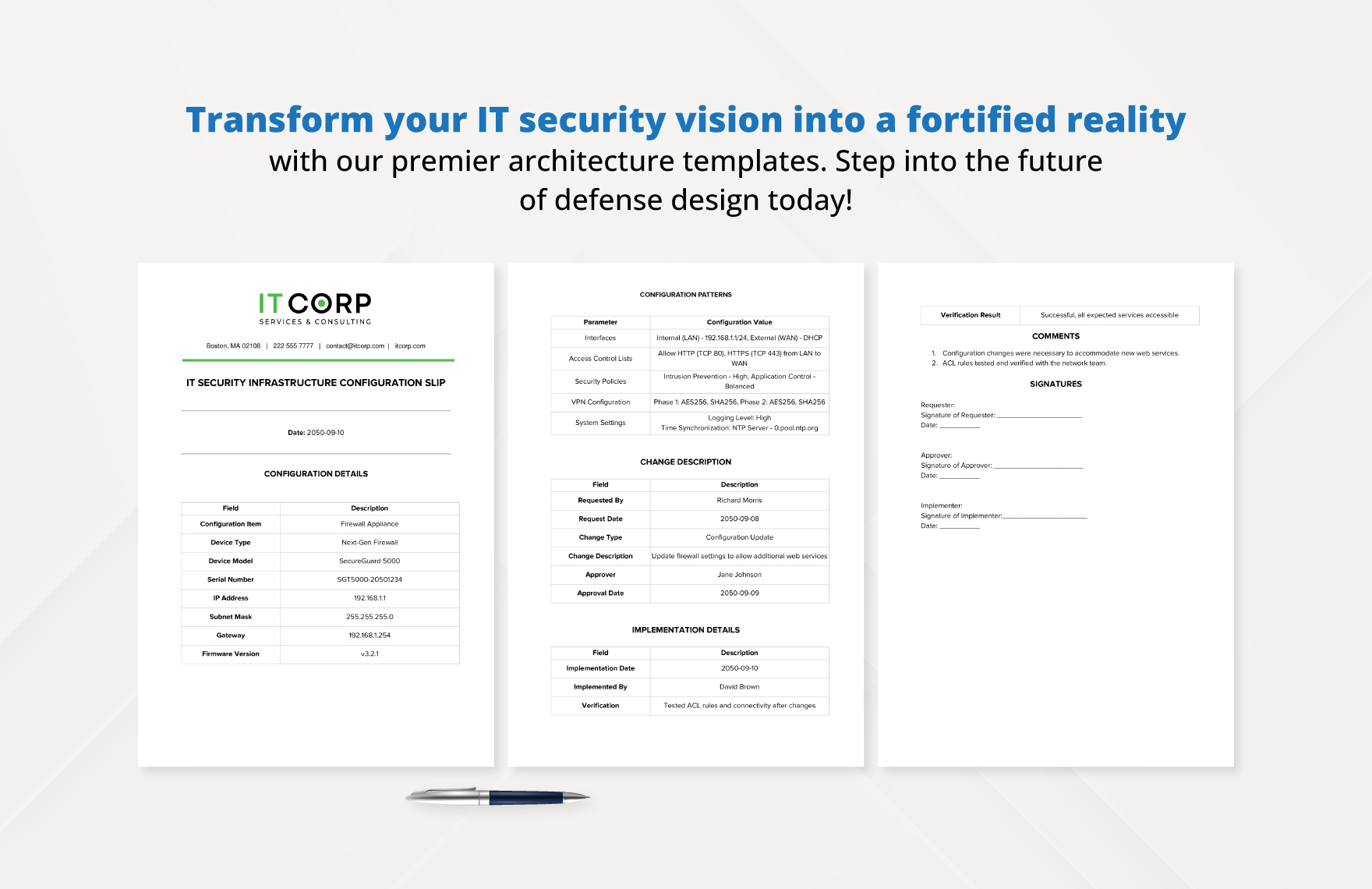
1. Implement Robust Encryption
Encryption is the process of converting data into a code that can only be deciphered with a specific key. Implementing robust encryption methods such as WPA3, AES, and SHA-256 can help prevent data breaches and cyber attacks.
2. Limit Access to Authorized Personnel
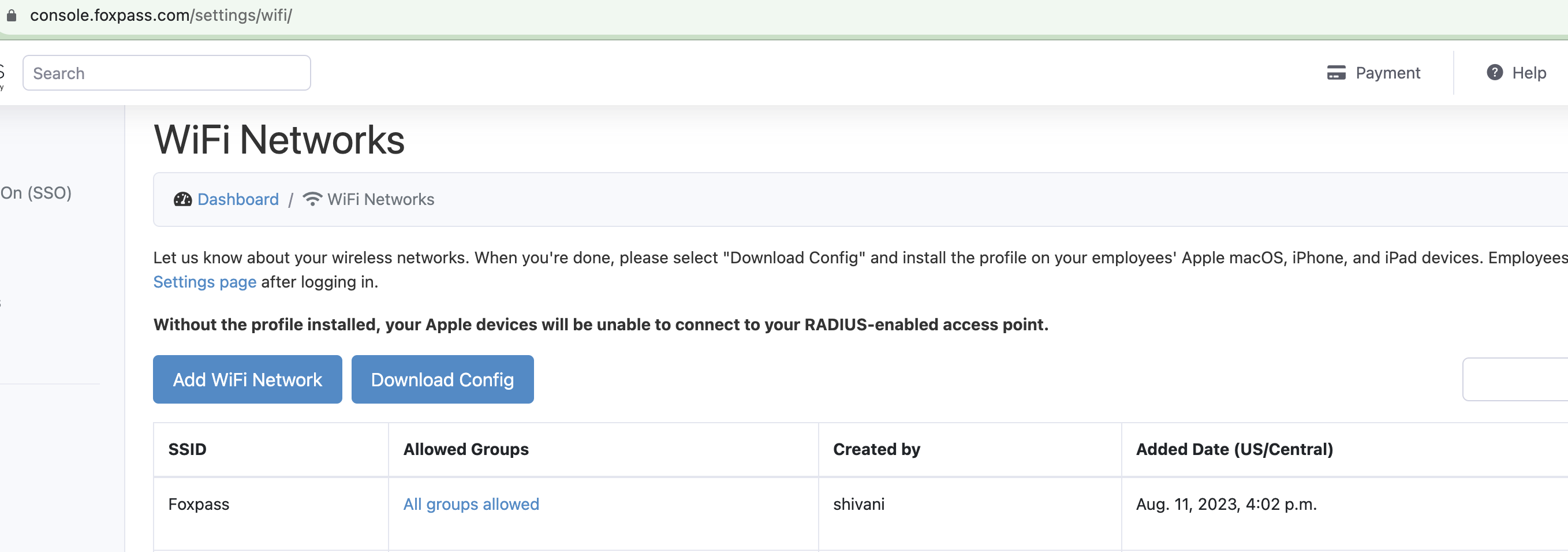
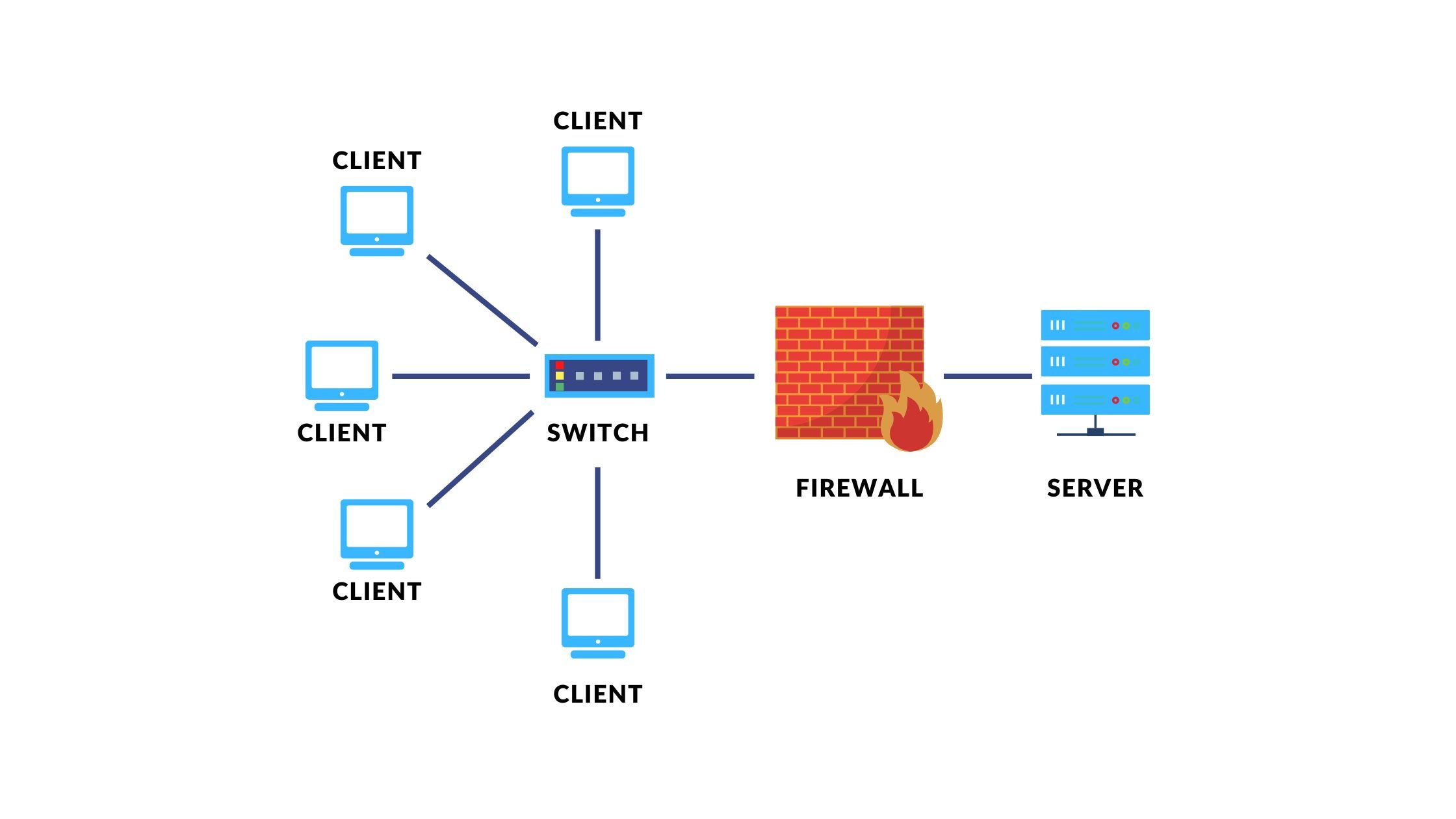
Limiting access to authorized personnel can help prevent unauthorized access to the wireless network. This can be achieved by using access control lists (ACLs) and implementing role-based access control (RBAC).




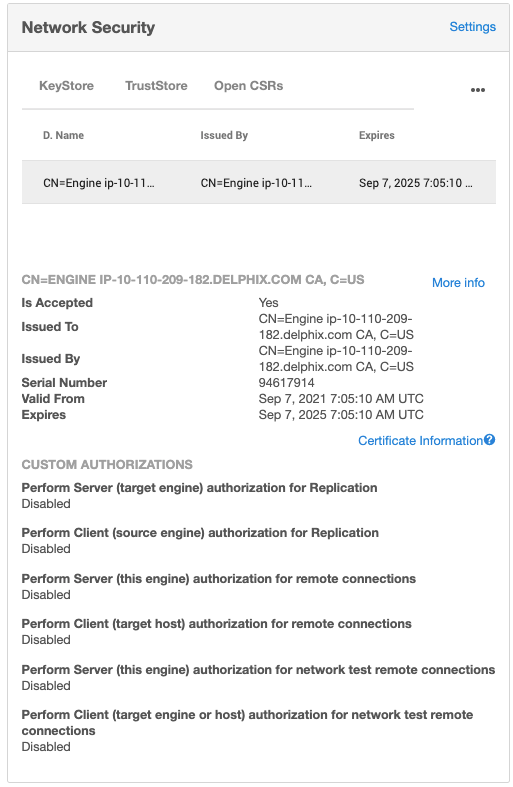









_IMAGE%20CTA%20%2B%20HOMEPAGE%20CAROUSEL%20-%20700x394.png?h=abce51c1&itok=uI75WP-f)