G DMZ Setup Configuration: A Comprehensive Guide to Secure Your Network
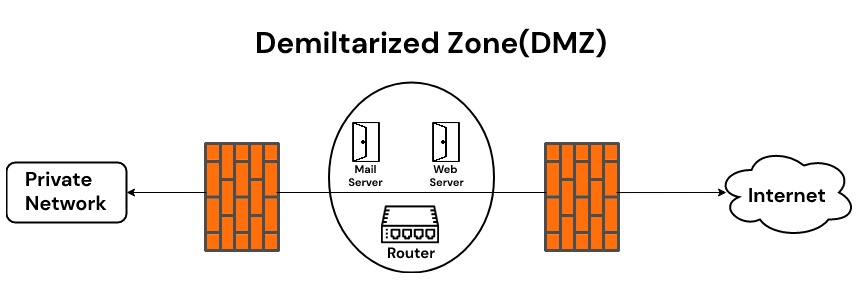
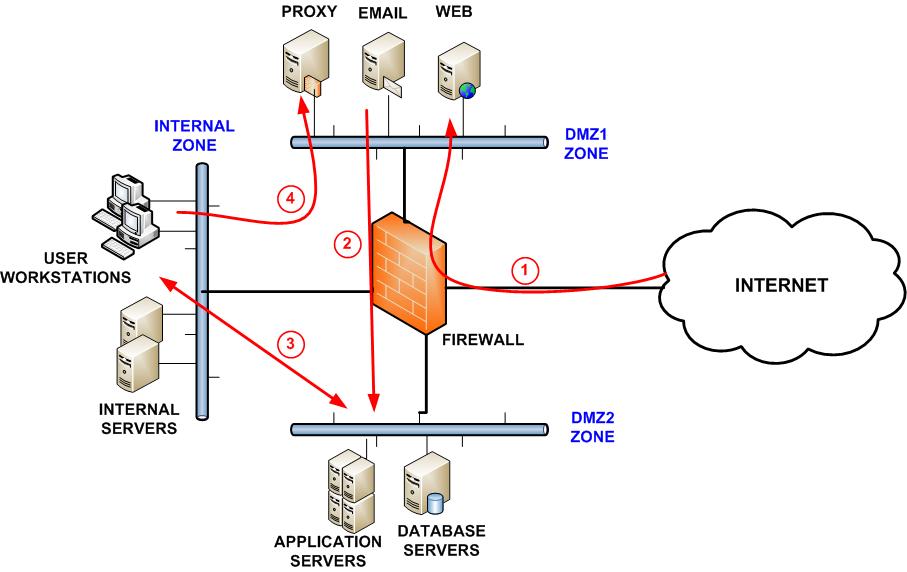
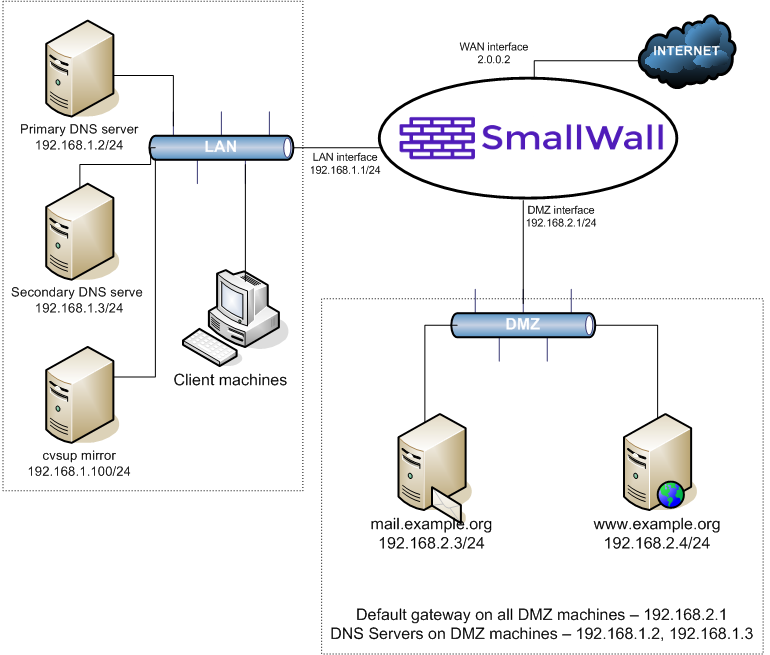
In today's digital age, network security is more crucial than ever. One effective way to protect your network is by implementing a demilitarized zone (DMZ) setup configuration. A DMZ is a network segment that separates public-facing services from your internal network, acting as a buffer zone between the two. In this article, we'll delve into the world of G DMZ setup configuration, exploring its benefits, requirements, and step-by-step setup process.
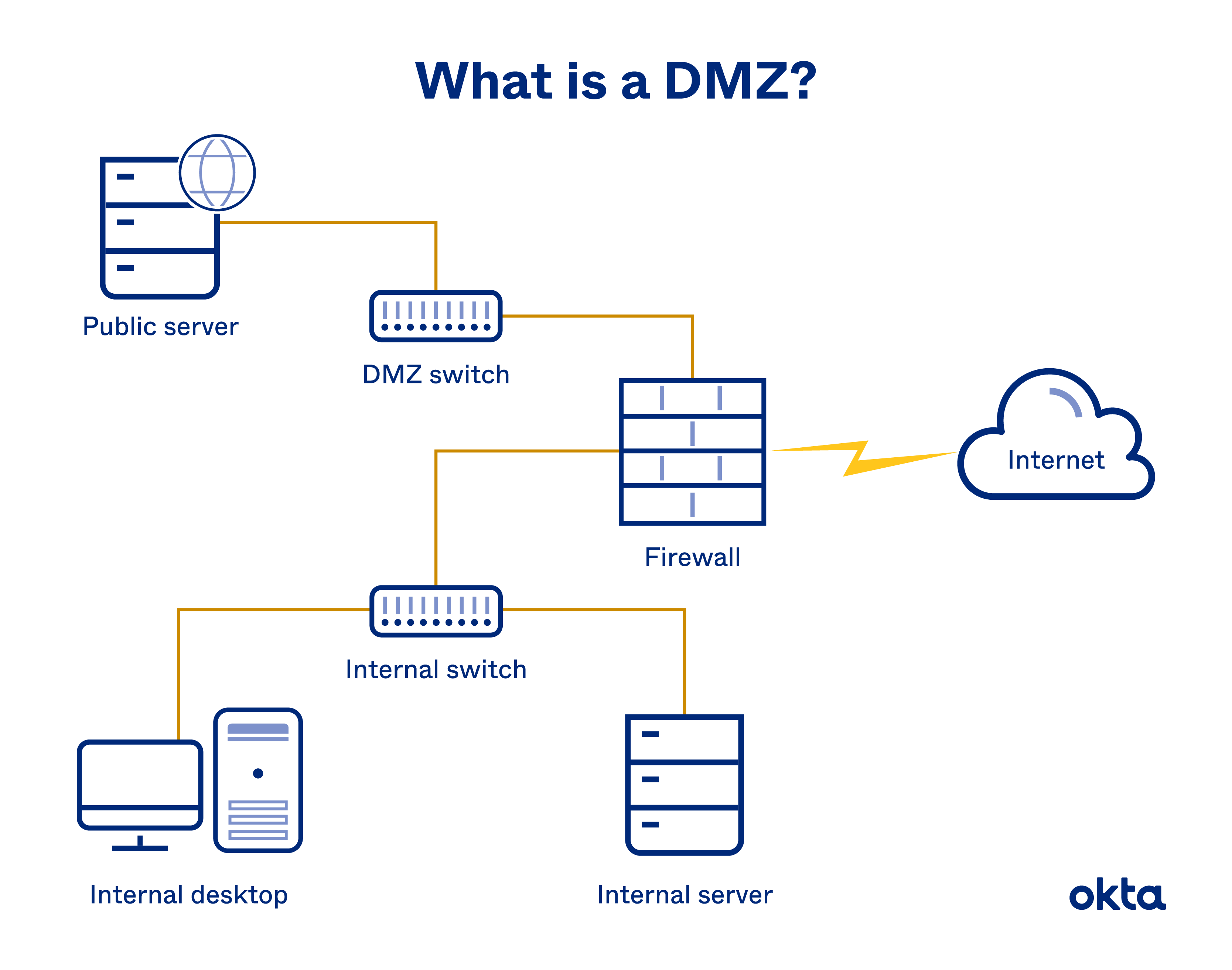
What is a DMZ?
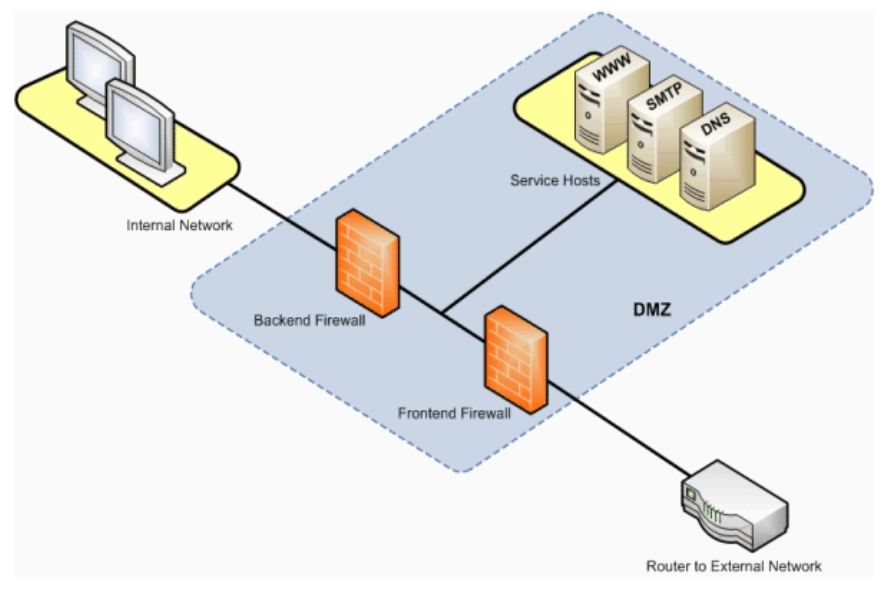
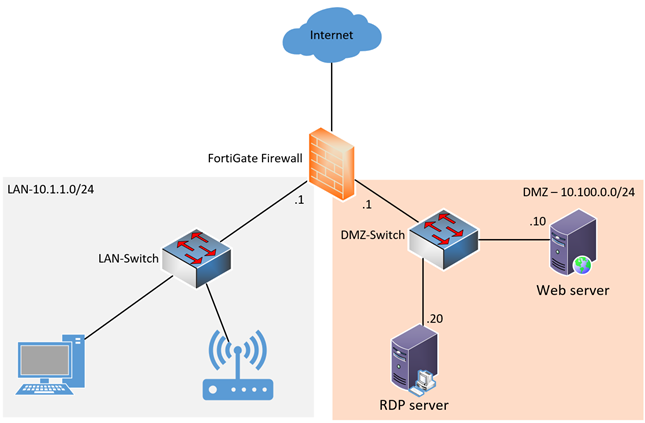
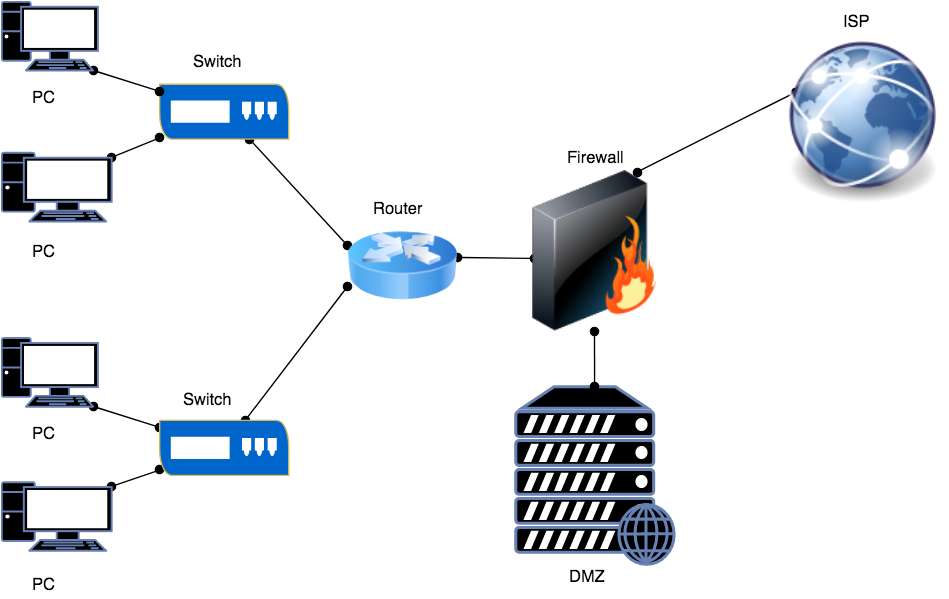
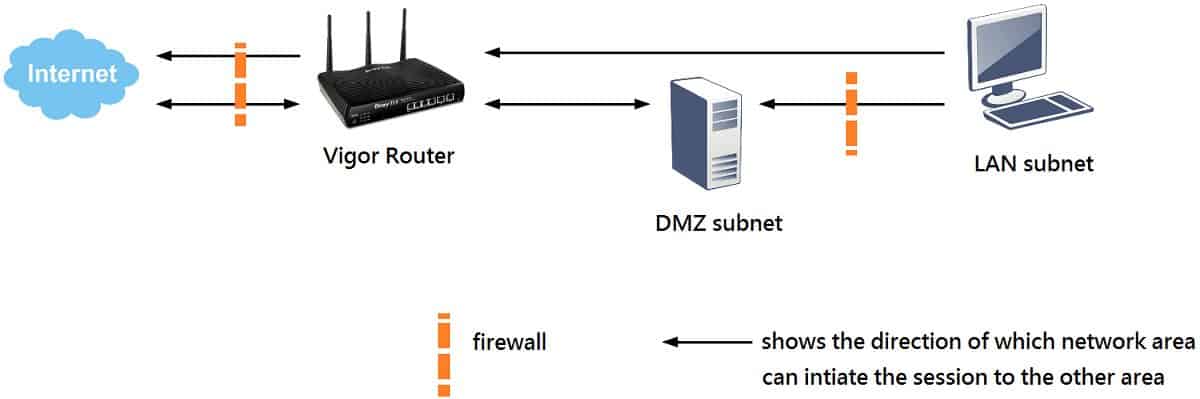
A DMZ is a network security concept that creates a neutral zone between your internal network and the external internet. It's a sub-network that's behind the firewall but open to the public. By placing your public services on a DMZ, you add an additional layer of security to your LAN (Local Area Network). A DMZ setup configuration is essential for organizations and individuals who want to protect their sensitive data and maintain a robust network security posture.
Benefits of a DMZ Setup Configuration
Improved network security: A DMZ setup configuration separates public-facing services from your internal network, reducing the risk of unauthorized access and potential breaches.
Enhanced compliance: By implementing a DMZ setup configuration, you can demonstrate your commitment to network security and compliance with industry regulations.
Reduced risk of cyber attacks: A DMZ setup configuration acts as a buffer zone between your internal network and the external internet, reducing the risk of cyber attacks and data breaches.
Easy management: A DMZ setup configuration allows for easy management of public services, making it simpler to update and maintain your network infrastructure.