G Network Security Setup for Secure Authentication: A Comprehensive Guide
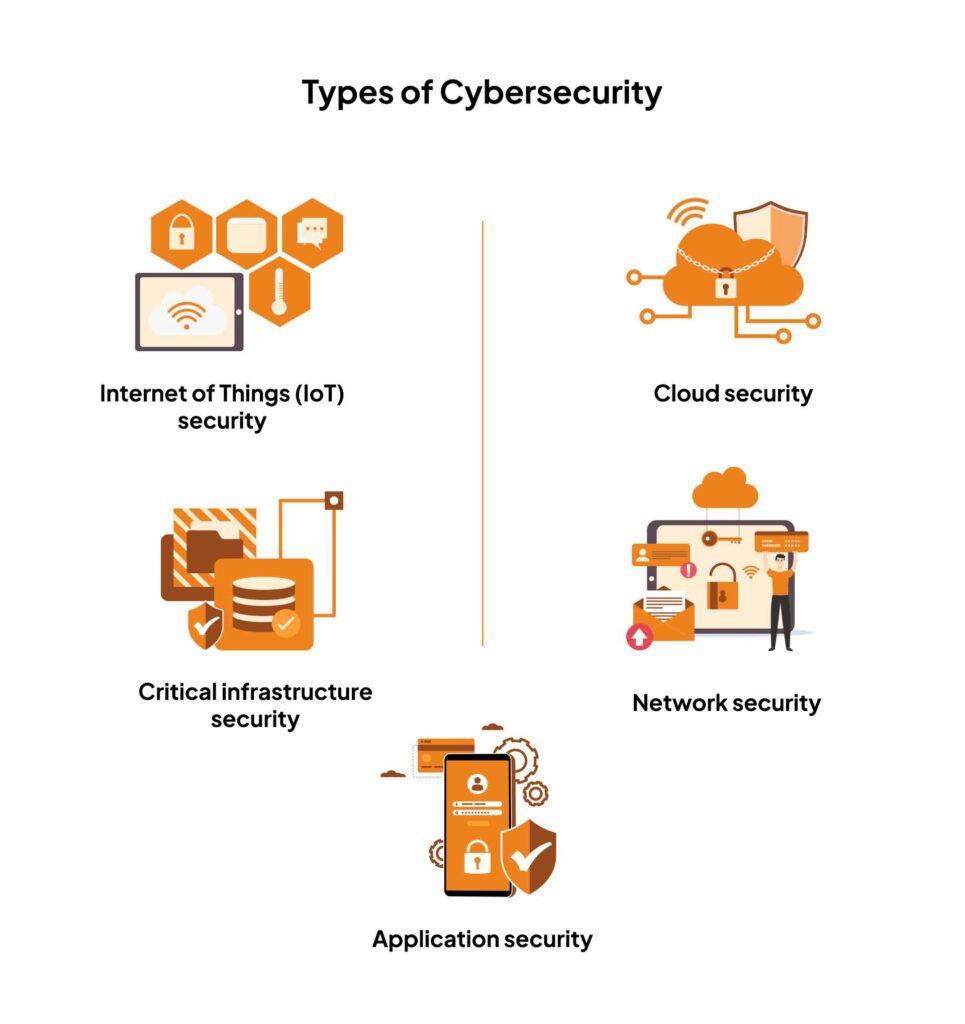
Network security is the backbone of any secure and efficient communication system. In today's digitized world, protecting sensitive information and preventing unauthorized access to your network is not just a good practice, but a necessity. A robust and secure network setup is crucial for preventing cyber threats and data breaches. In this article, we'll discuss G Network Security Setup for Secure Authentication and explore the various elements and components that are essential for creating a secure and reliable network.
What is G Network Security Setup?
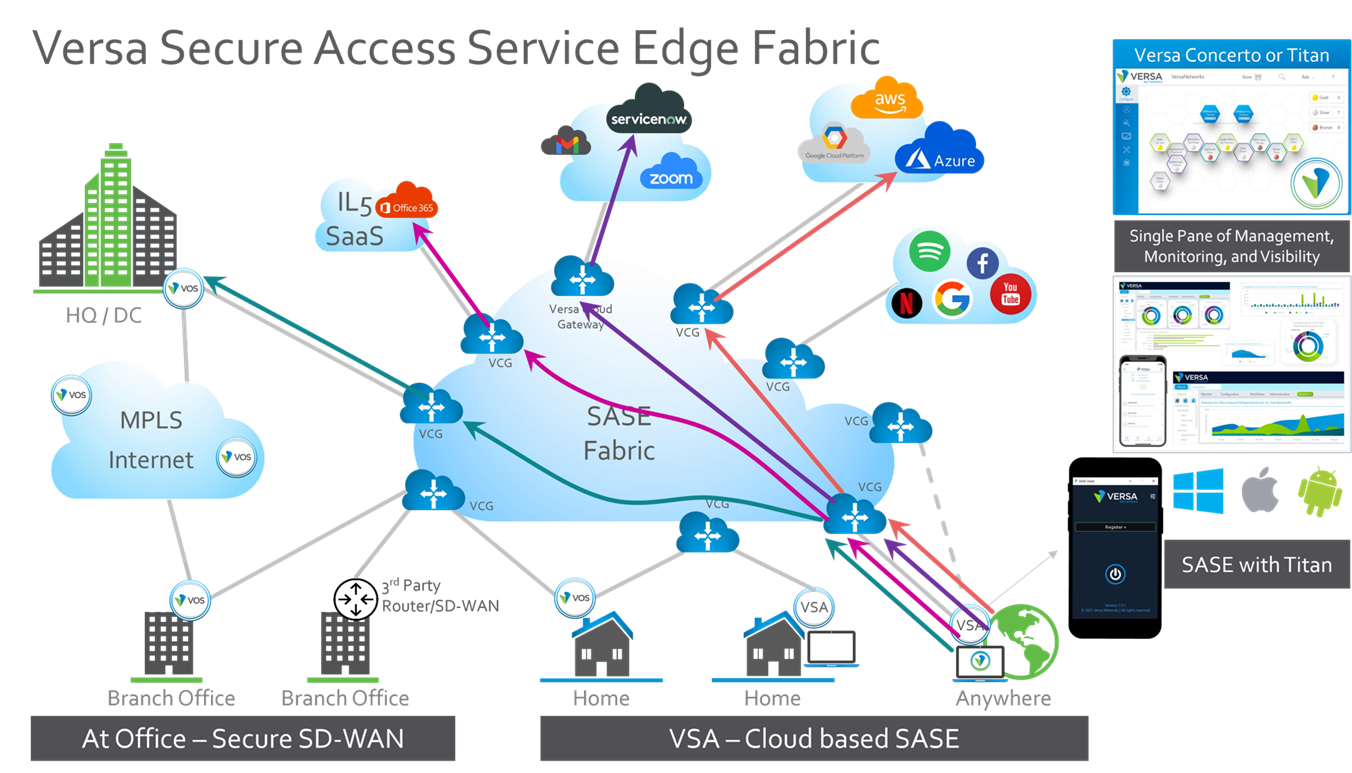
G Network Security Setup is a comprehensive security framework that ensures the safe and secure transportation of data between users, applications, and servers over the network. This setup involves a combination of hardware, software, and network configurations that work together to prevent unauthorized access, data breaches, and other cyber threats.

_key Components of G Network Security Setup
- Authentication**: The process of verifying the identity of users and devices that connect to the network. This includes multi-factor authentication (MFA) and other advanced authentication methods like biometrics and smart cards.
- Authorization**: The process of granting or denying the rights and permissions to access certain network resources and applications based on user identity and group membership.
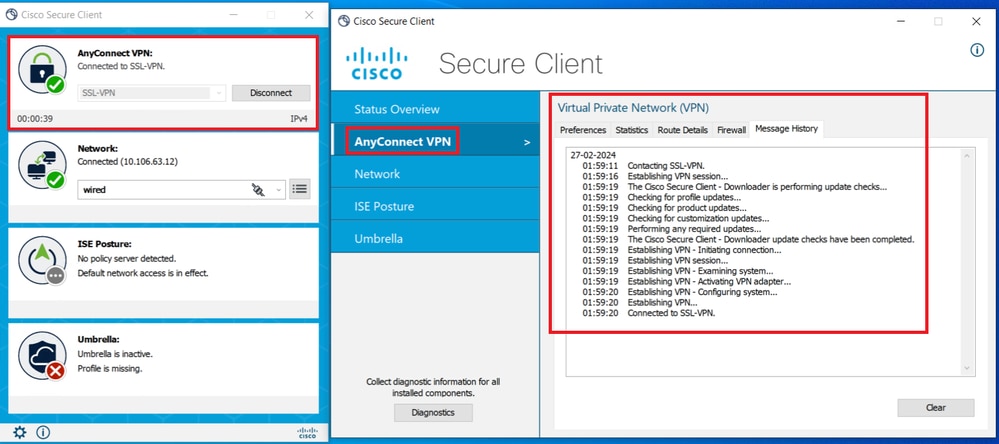
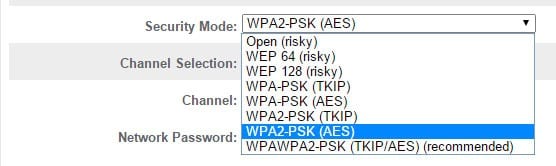
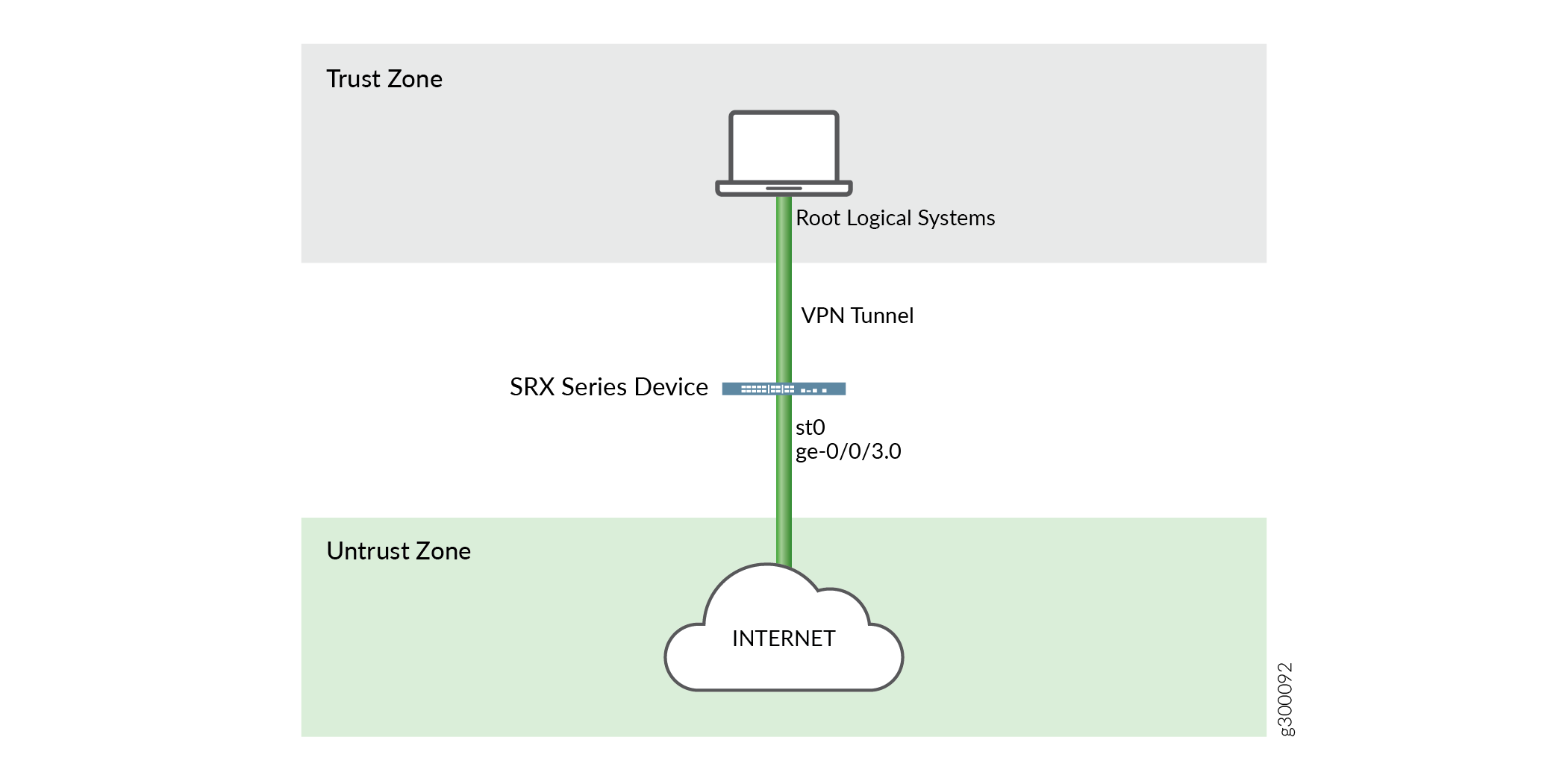
- Encryption**: The process of converting plaintext data into unreadable cipher text using algorithms like AES, SSL/TLS, and VPNs to prevent eavesdropping and interception of sensitive information.
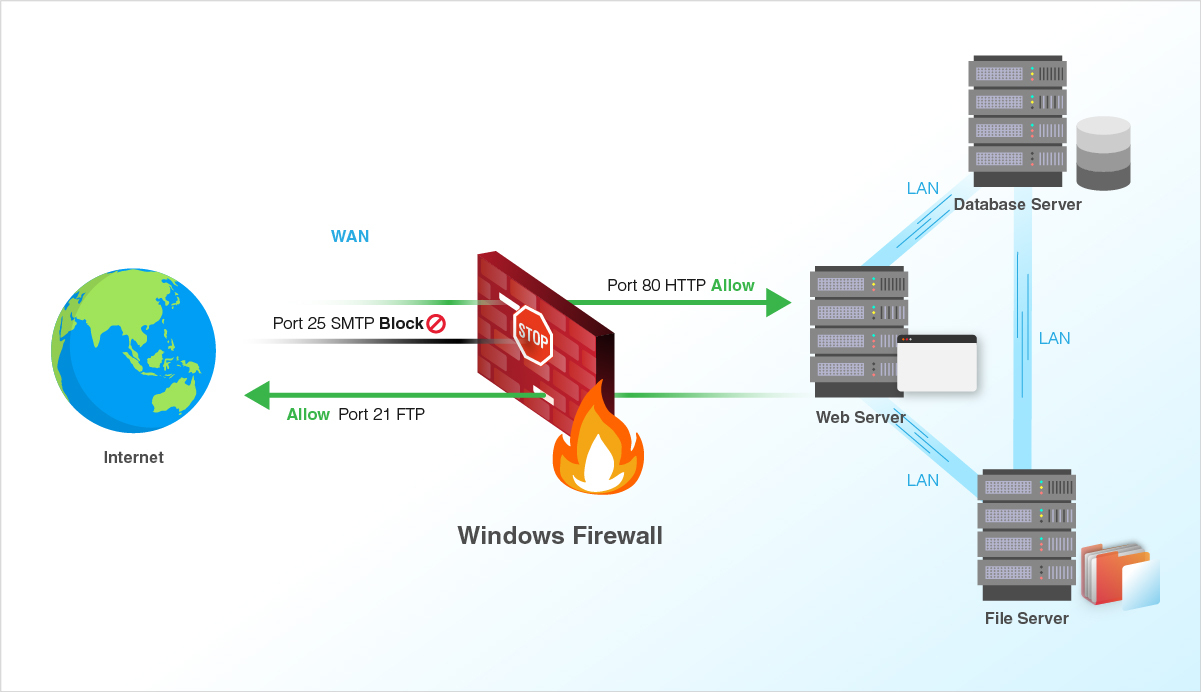
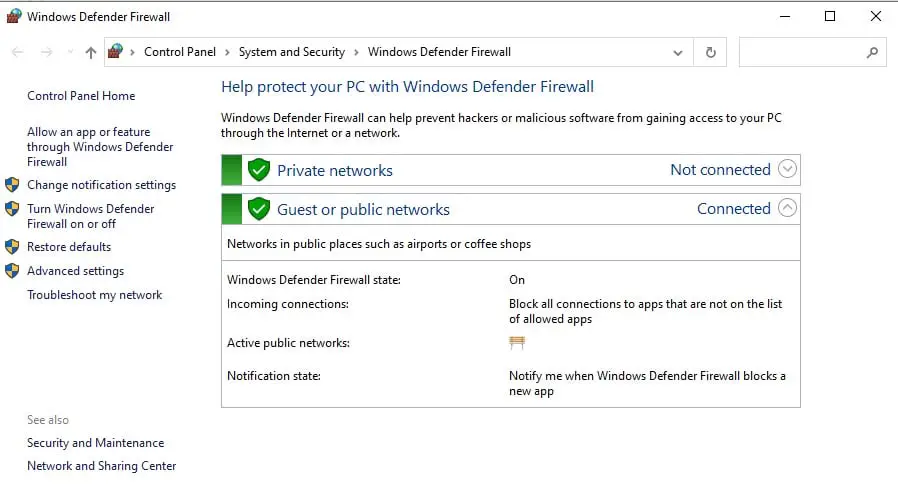
- Firewall**: A network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules and policies.
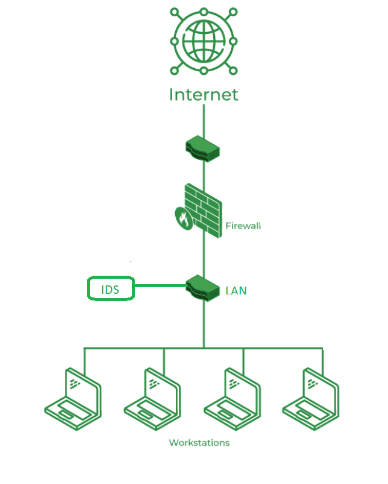
- Network Intrusion Detection Systems (NIDS)**: A security system that monitors network traffic for signs of unauthorized access or malicious activity.
- Access Control Lists (ACLs)**: A set of rules that determine which users and devices are allowed to access specific network resources and applications.