G Network Configuration for Continuous Monitoring
As the world becomes increasingly dependent on technology, the need for continuous monitoring of network configurations has never been more pressing. In this article, we will explore the importance of G network configuration for continuous monitoring and provide a comprehensive overview of the benefits and best practices involved.
What is G Network Configuration for Continuous Monitoring?
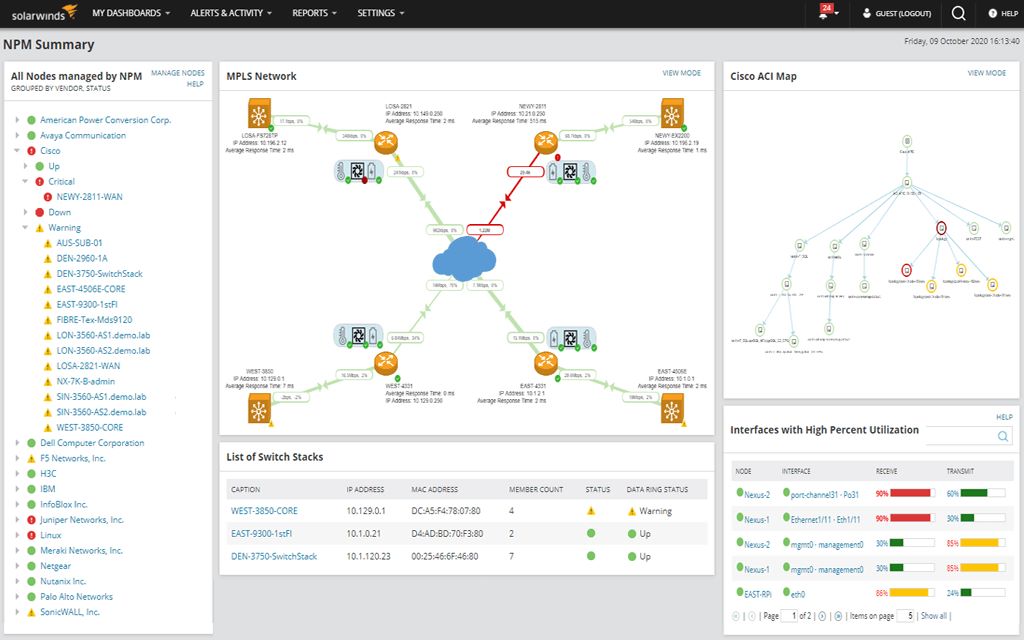
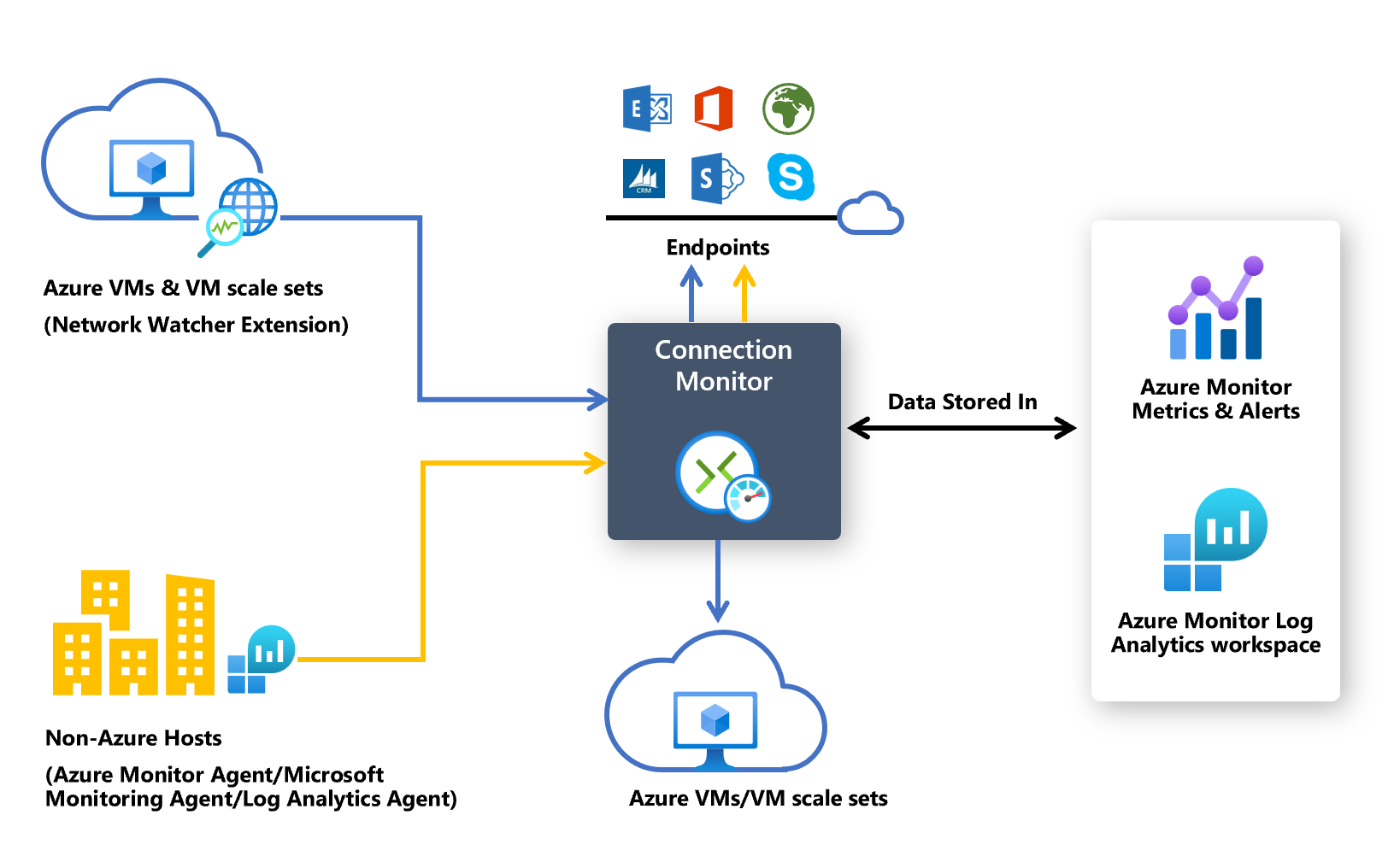
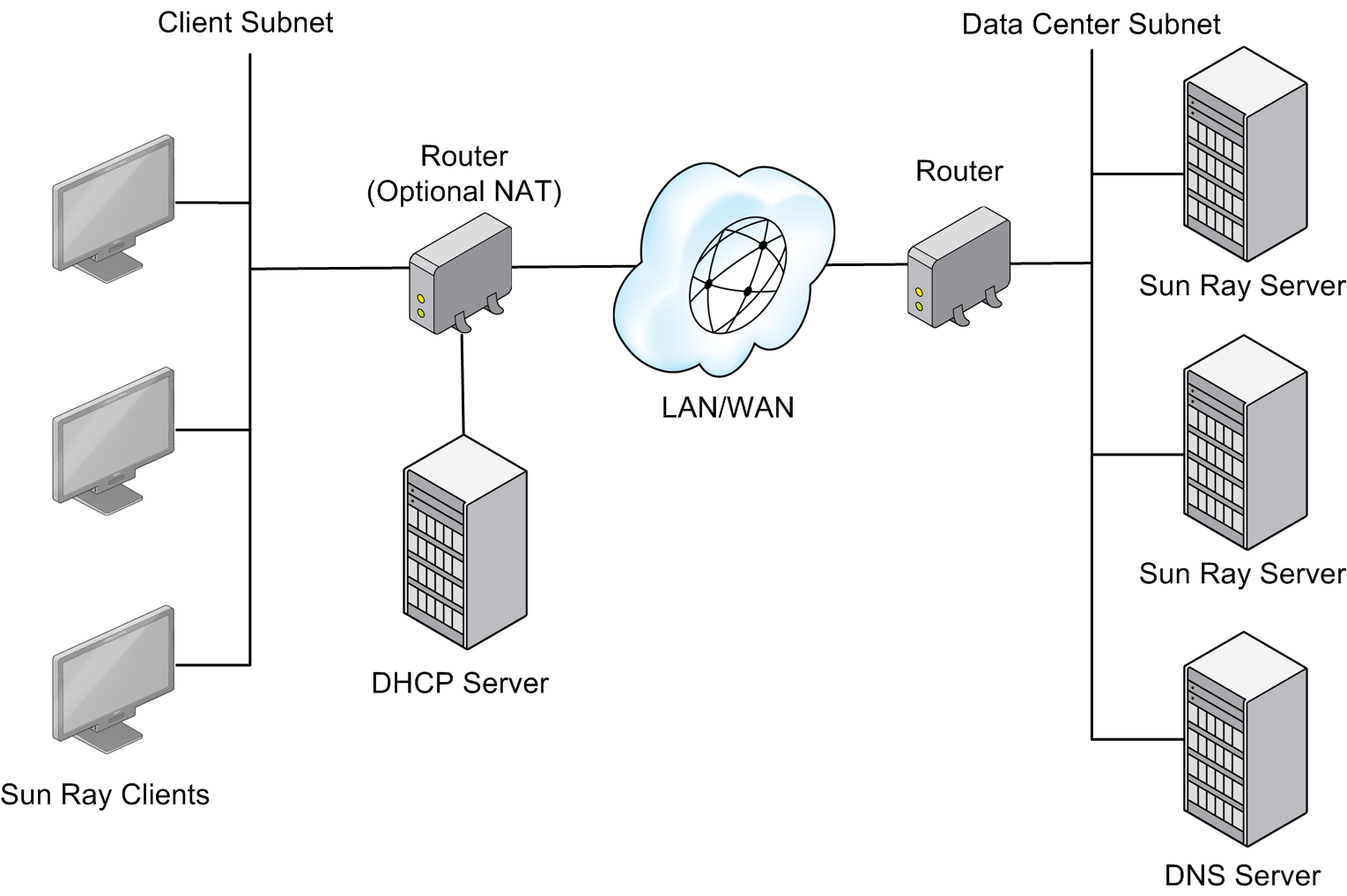
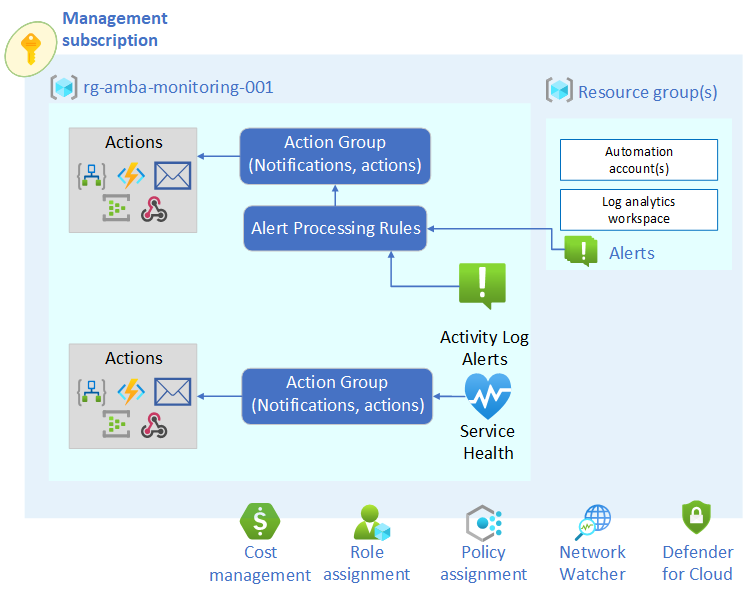
Continuous monitoring is the process of constantly observing and analyzing various elements of an organization's IT and information security systems, including network security, system downtime, compliance, and operational efficiency. G network configuration for continuous monitoring involves setting up a network configuration that enables real-time visibility into vulnerabilities and allows for quick identification and mitigation of security threats.
Benefits of G Network Configuration for Continuous Monitoring
The benefits of G network configuration for continuous monitoring are numerous. Some of the most significant advantages include:
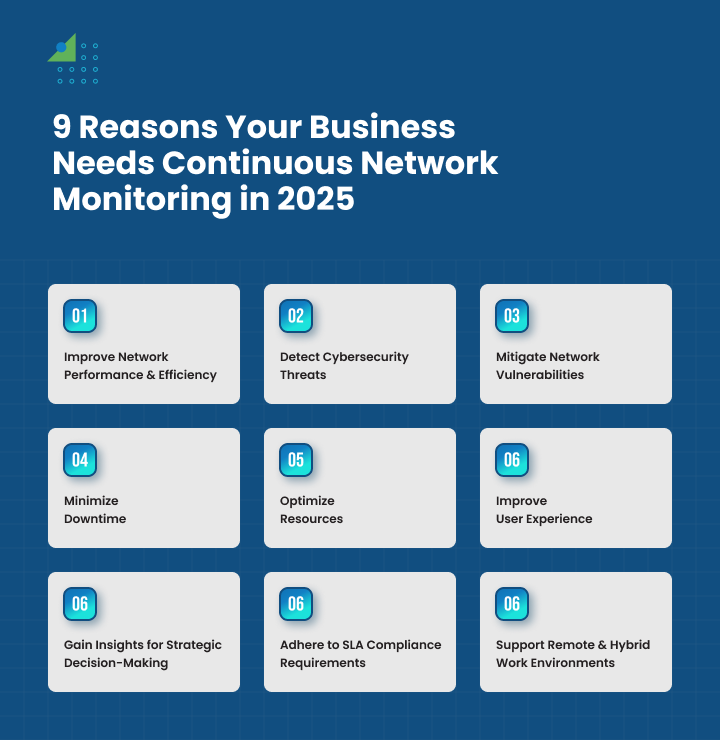
- Real-time visibility into vulnerabilities
- Quick identification and mitigation of security threats
- Reduced downtime and increased system availability
- Improved compliance with regulatory requirements
- Enhanced operational efficiency and reduced costs
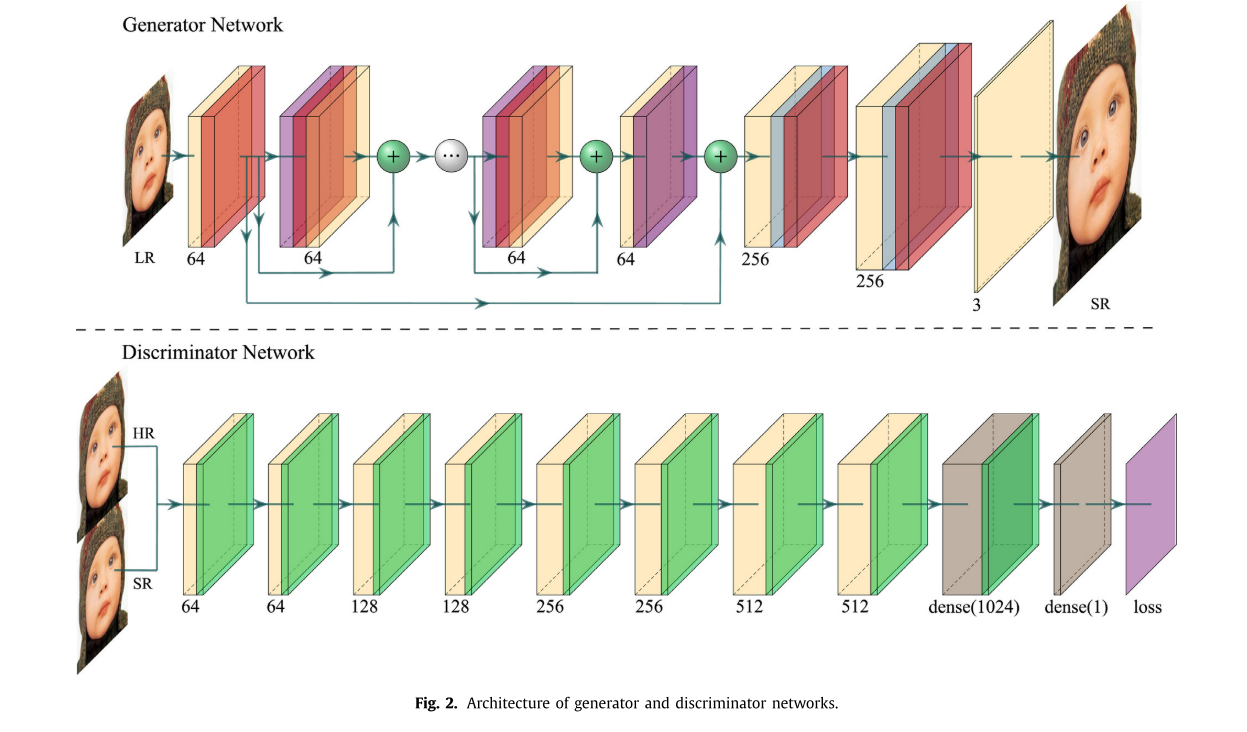
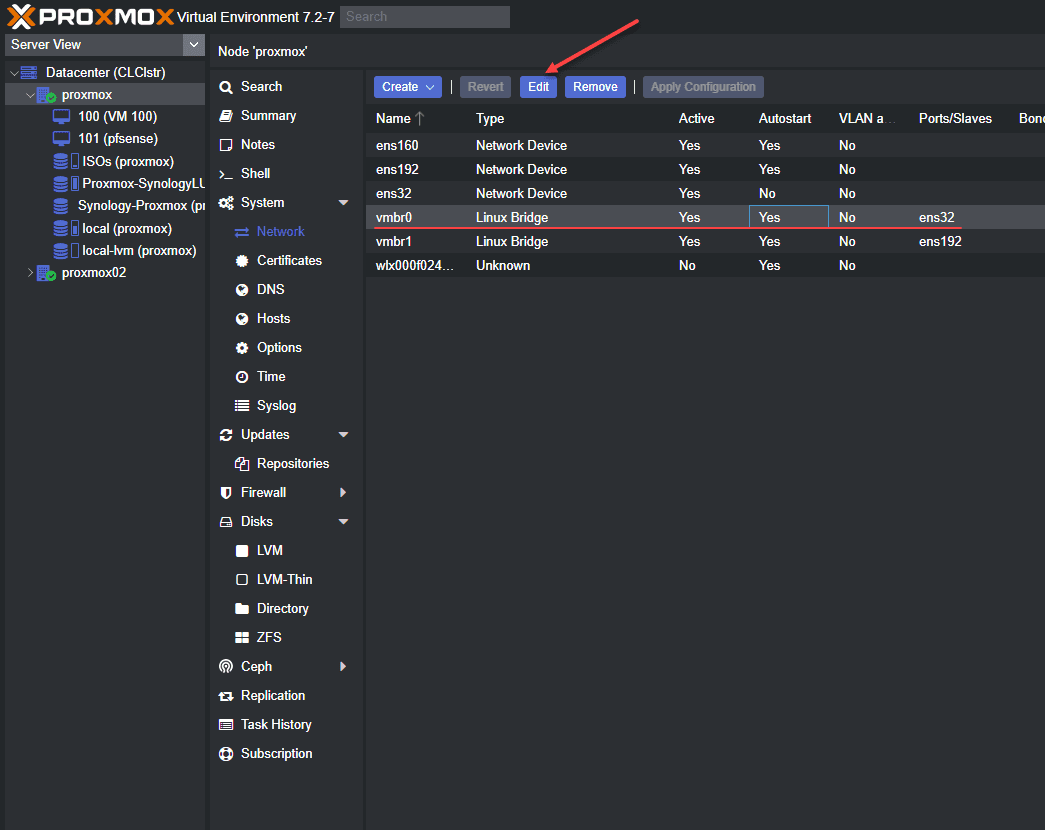
Key Components of G Network Configuration for Continuous Monitoring
There are several key components that are essential for G network configuration for continuous monitoring. These include:
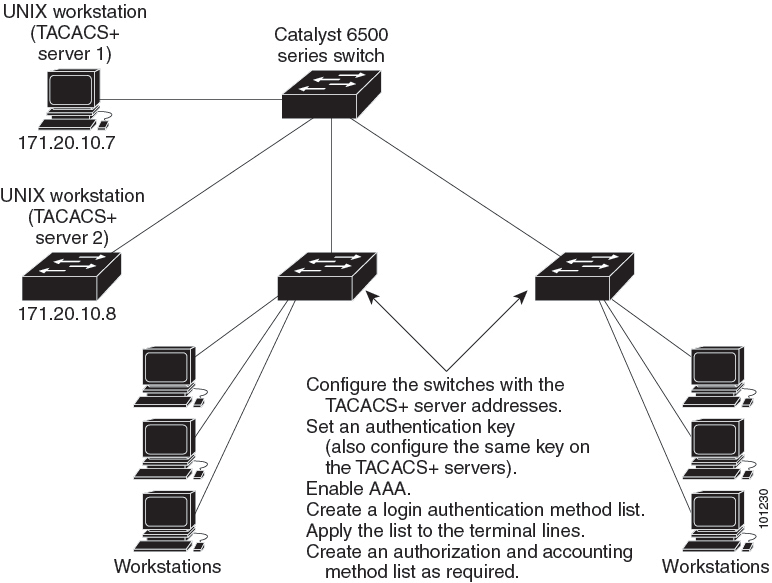
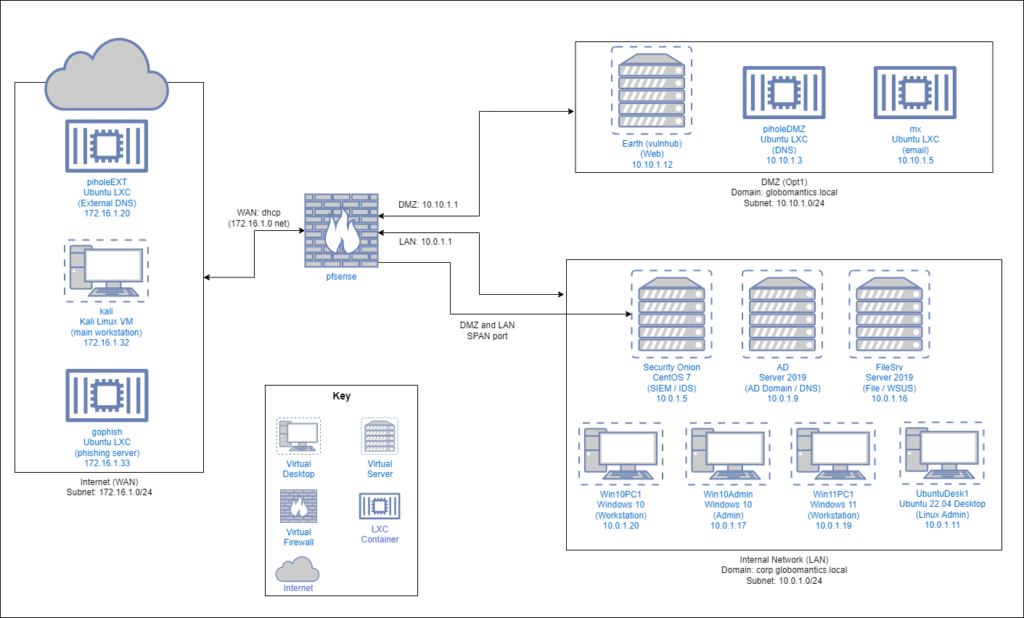
- Network device enumeration: This involves identifying and documenting all network devices on the network, including their configuration and settings.
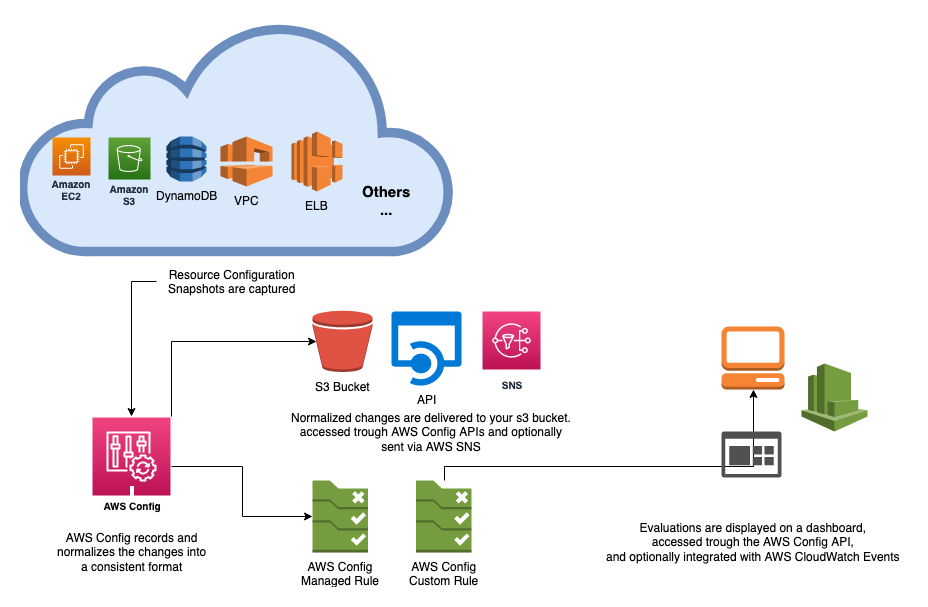
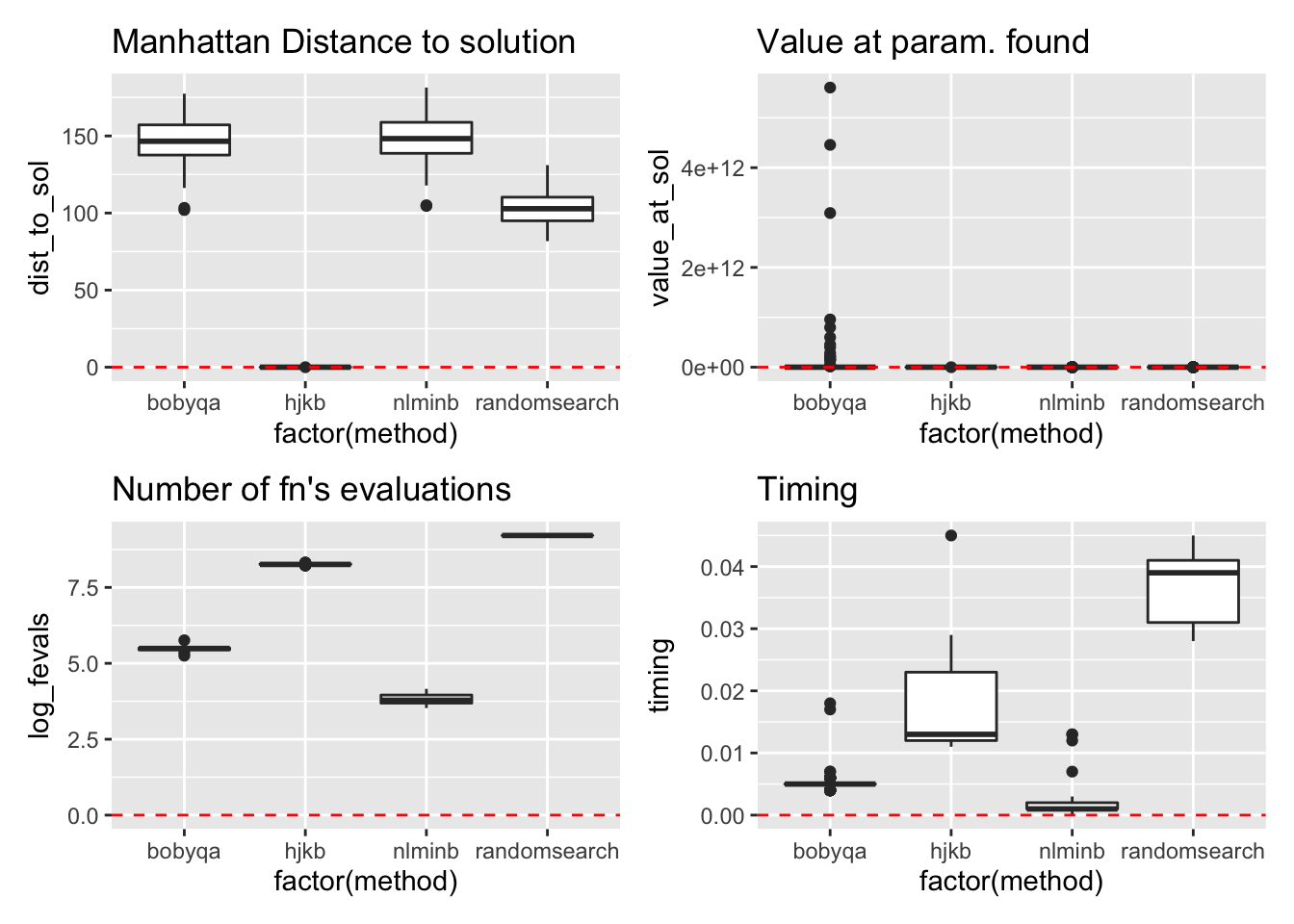
- Automated vulnerability scanning: This involves using automated tools to scan the network for known vulnerabilities and identifying areas for improvement.
- Continuous auditing: This involves using automated tools to regularly audit network configurations and settings to ensure compliance with security policies and regulatory requirements.
- Real-time monitoring: This involves using tools to constantly monitor network activity and identify security threats in real-time.
- -menagement: This involves establishing a process for managing changes to network configurations and ensuring that all changes are properly documented and approved.